Portfolio
Penetration Testing
Uncover vulnerabilities
before attackers exploit them.
Introduction
Penetration Testing is a proactive security assessment designed to simulate real-world cyberattacks on your systems, applications, and infrastructure. By identifying security gaps before malicious actors do, your organization gains the insight needed to strengthen defenses and reduce risk. Our expert team uses industry-leading methodologies and advanced tools to reveal weaknesses that traditional security measures often miss.
Beyond detection, we provide strategic recommendations that help you understand the impact of each vulnerability and prioritize remediation. Whether you manage websites, cloud environments, internal networks, or critical business systems, our penetration testing service ensures you operate with confidence, resilience, and stronger protection against emerging threats.
Identify hidden vulnerabilities
Enhance your security posture
Meet compliance requirements
Strengthen resilience
Our Testing Approach
Our penetration testing process follows globally recognized standards such as OWASP, NIST SP 800-115, and PTES. We combine automated scanning with deep manual testing to ensure we uncover both common and advanced vulnerabilities, including misconfigurations, logic flaws, privilege escalation paths, broken access control, and insecure integrations. Each engagement is tailored to your systems and business operations so that the assessment reflects realistic attack scenarios specific to your environment.
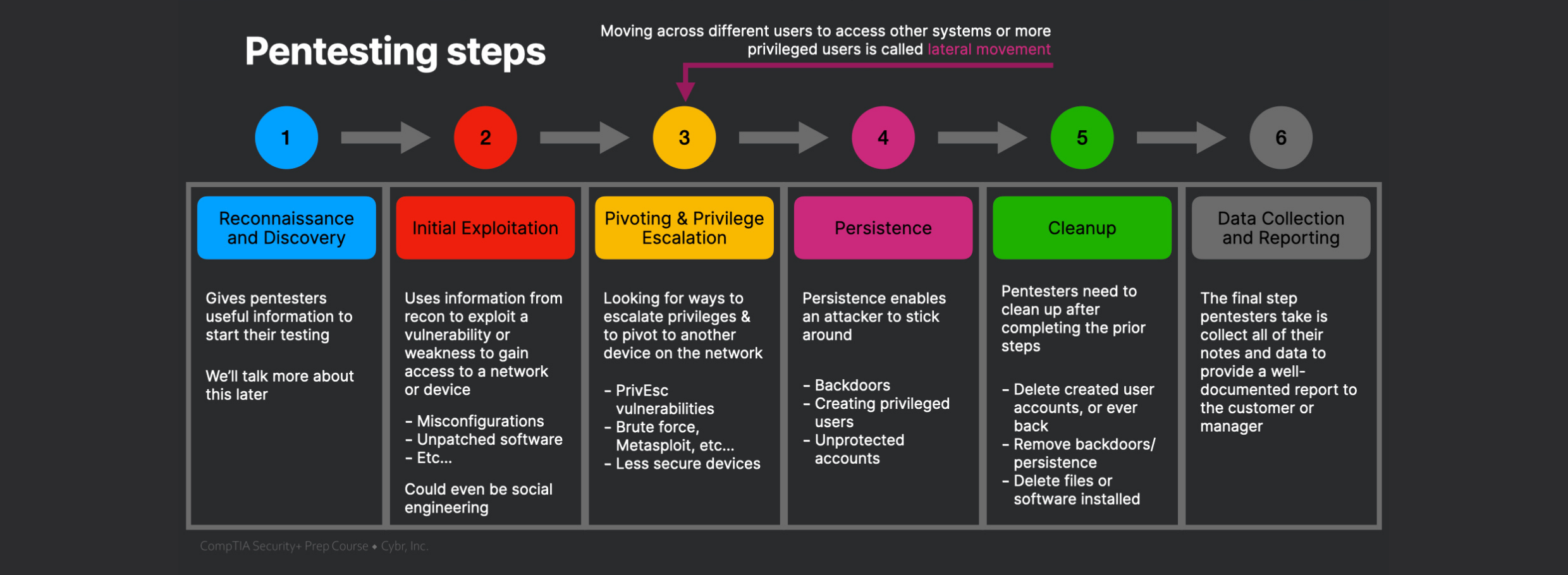
We also perform thorough exploitation and post-exploitation steps—always within the approved scope—to demonstrate the real-world impact of vulnerabilities. This gives you a practical understanding of how an attacker could move through your environment, extract sensitive data, or disrupt services. Our goal is not just to identify issues but to help you see how they could be used against your business.
Detailed Reporting & Remediation Guidance
At the end of the engagement, you receive a comprehensive, easy-to-understand report that includes executive summaries for leadership and technical findings for your IT and security teams. Each vulnerability is categorized based on risk level, business impact, and likelihood of exploitation. We also highlight quick wins and long-term improvements to help you strengthen your cybersecurity posture effectively.
In addition, we offer follow-up consultations to walk you through the findings, clarify technical details, and support your remediation efforts. This ensures your team fully understands each risk and has clear steps to resolve it. Our goal is to empower your organization to achieve continuous security improvement—not just pass a test.
Strengthen Your Security with Proven Expertise
Our certified cybersecurity professionals deliver accurate, thorough, and real-world penetration testing to help you protect what matters most.

From concept to launch, we create intuitive apps that enhance engagement.
02

Your Benefits
Why Choose Fort Pentesting
for Your Security Needs?
We combine advanced testing methodologies with practical,real-world
insights to help your business stay ahead of evolving cyber threats.
Certified Ethical Hackers
Comprehensive Testing Coverage
Clear, Actionable Reporting
Support Beyond the Test
Contact Us
Connect with us for best solutions
and success.
Our team is ready to assist you with expert guidance, tailored recommendations, and reliable support for all your cybersecurity and IT needs.
Schedule an appointment with us today!
Keep up with the dynamic world of IT operations,
and stay ahead with cutting-edge solution.
-
Emails
-
Phone
-
Location
-
Follow us on
