Cybersecurity
Vulnerability Assessment
Identify security weaknesses before they become serious threats.
Introduction
A Vulnerability Assessment provides a comprehensive review of your systems, networks, and applications to detect weaknesses that attackers could exploit. Unlike penetration testing—which simulates active attacks—this service focuses on thorough discovery, classification, and prioritization of vulnerabilities across your entire environment. It gives you a clear, accurate picture of your current security posture.
Our assessment is performed using industry-standard tools, expert analysis, and proven methodologies such as OWASP, NIST, and CIS Benchmarks. We evaluate misconfigurations, weak controls, outdated software, insecure system settings, and exposure to known threats. With detailed insights and prioritized recommendations, your business can take proactive steps to strengthen security before attackers find a way in.
Comprehensive visibility
Prioritized remediation guidance
Continuous security improvement
Improved compliance readiness
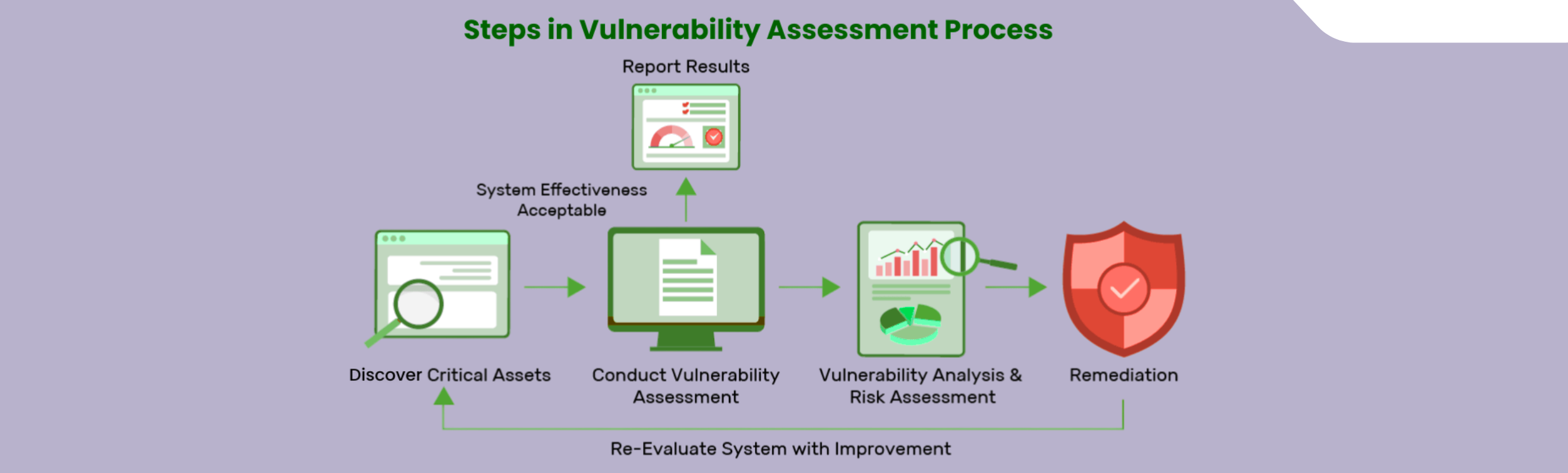
Our Assessment Methodology
Our vulnerability assessment process combines automated scanning with manual verification to ensure findings are accurate and actionable. We identify common issues such as unpatched software, weak configurations, insecure services, outdated protocols, and exposed assets. Each vulnerability is validated to reduce false positives and ensure your team receives reliable results that can be acted on with confidence.

We tailor the assessment scope to your specific environment—whether it's on-premise, cloud, hybrid, or application-based. This ensures that every component of your infrastructure is evaluated against the latest threat intelligence and security best practices.
Detailed Reporting & Risk Recommendations
Upon completion, we provide a detailed report that includes a risk rating for each vulnerability, its potential impact, likelihood of exploitation, and clear steps to fix it. The report is structured for both technical teams and non-technical stakeholders, ensuring everyone understands the risks and the actions required to mitigate them.
We also deliver a debriefing session to walk your team through the findings, answer questions, and offer guidance on prioritizing remediation. Our goal is to support your organization in building a sustainable and effective vulnerability management program

Gain Complete Visibility Into Your Security Risks
Our vulnerability assessments reveal weaknesses across your systems, helping you secure your digital environment with confidence

From concept to launch, we create intuitive apps that enhance engagement.
02

Your Benefits
Why Choose Us for
Vulnerability Assessment?
We deliver precise, reliable, and timely assessments backed by
expert analysis and ongoing support.
Accurate and validated results
Industry-standard assessment methodologies
Clear, practical remediation steps
Continued support and follow-up assessments
Contact Us
Connect with us for best solutions
and success.
We enhanced speed and design for a better user experience
Schedule an appointment with us today!
Keep up with the dynamic world of IT operations,
and stay ahead with cutting-edge solution.
-
Emails
-
Phone
-
Location
-
Follow us on
